Hacking Cybermaggedon: How to Prevent the End of the World as We Know It
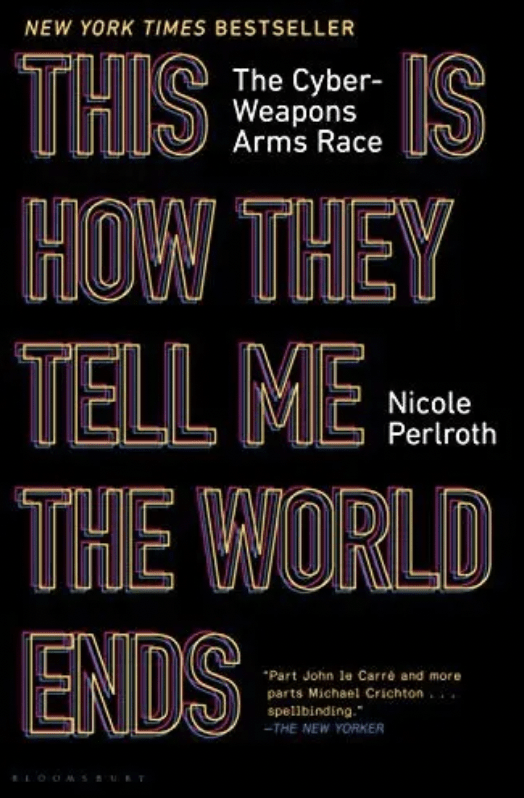
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
By Nicole Perlroth
Bloomsbury/2021
reviewed by Colin Robertson
POLICY MAGAZINE July 13, 2022
The 15-hour Rogers’ shutdown of July 8th and its impacts – on everything from buying groceries to banking, border entry and 911 – reminded us of the extent to which our lives now depend on cyber-connectivity.
Now, at government direction, Canadian telecoms are scrambling to come up with better redundancy and resiliency plans. It is time well spent. For their homework, they may also want to read Nicole Perlroth’s engagingly depressing book, This Is How They Tell Me the World Ends: The Cyberweapons Arms Race.
For over a decade, Perlroth was the lead cybersecurity reporter at The New York Times. This is How They Tell Me the World Ends draws on more than 300 interviews as well as her investigative reporting. Her stories, which often read like spy thrillers, detailed Russian hacks of nuclear plants, airports, elections, and petrochemical plants. She revealed North Korea’s cyberattack against Sony Pictures, Bangladesh banks and crypto exchanges, as well as Iranian attacks on oil companies, banks and dams. Then there were (and continue to be) the thousands of Chinese cyberattacks against western businesses, including the Chinese hack of The New York Times.
Perlroth’s stories led the US Department of Justice to file hacking charges against the Chinese military. This Is How They Tell Me the World Ends won both the McKinsey and Financial Times’ 2021 “Business Book of the Year Award.” Perlroth left the Times last year to join the Department of Homeland Security’s Cybersecurity Advisory Committee.
This book was highly recommended by friends who work on cyber-threats but each time I dove into it I pulled away because while it reads like a spy thriller, it’s all true. It scared the bejeezus out of me, so I set it aside for the fictional spy tales of Ted Allbeury, Anthony Price and Helen MacInnes. The hacking of my Twitter account and the Rogers shutdown prompted me to reconsider. As Perlroth observes, time and again, we need to understand our cyber-vulnerabilities and then prepare for them.
One of the better satirical commentaries arising out of the Rogers debacle was the tongue-in-cheek Beaverton headline: “Putin determines cyber-attack against Canada not necessary since Rogers is far more effective”. But as Perlroth details, the threat from Russia, China, Iran, North Korea and other rogue actors is no joke. Having basically automated and digitized our entire economies, the West has a very soft underbelly when it comes to cyber. As we’ve all known for nearly two decades, digital connectivity creates a vast target field for remote, anonymous sabotage, as we have witnessed with attacks on hospitals and pipelines.
Perlroth starts with a 2019 trip to Ukraine to learn more about the Russian cyberattack that was timed to coincide with Ukraine’s Constitution Day in 2017. It shut down government agencies, railways, ATMs, gas stations, as well as the radiation monitors at the Chernobyl nuclear site. The collateral damage closed factories in Tanzania, destroyed vaccines, infiltrated computers at FedEx and brought Maersk, the world’s biggest shipping conglomerate, to a halt.
The hackers were Russian, cheered on and directed by Vladimir Putin, who had told a gaggle of reporters just prior to the attack that “if they have patriotic leaning, they may try to add their contribution to the fight against those who speak badly about Russia.” The crux of Russian foreign policy, shared with Xi Jinping’s China and spelled out in their February 2022 entente, is to undercut the West, and the rule of law that underwrites our global institutions. As Russian Foreign Minister Sergey Lavrov has admitted and Perlroth reiterates: “We might have seen that the end game wasn’t Ukraine. It was us.” We are even more exposed, says Perlroth, as offensive cyber-technology leaves those responsible for defence constantly playing catch-up. For Perlroth: “The Ukranians knew it. Our enemies knew it. The hackers had always known it. This is how they tell me the world ends.”
This book was recommended by friends who work on cyber-threats but … it scared the bejeezus out of me, so I set it aside for the fictional spy tales of Ted Allbeury, Anthony Price and Helen MacInnes. The hacking of my Twitter account and the Rogers shutdown prompted me to reconsider.
So, what can we do to mitigate our vulnerabilities, recognizing that it is now arguably easier for a rogue actor to sabotage the software embedded in an airliner than to hijack it? Perlroth offers these cautions and recommendations:
First, a global cyber-arms race is in full swing. Russia, China, North Korea, and Iran are stockpiling their weaponry. They know our digital topography well. In too many cases, they are already inside.
Second, digital vulnerabilities that affect one, affect us all. Our infrastructure is now virtualized, and only becoming more so as the pandemic thrusts us online as never before. More Canadians – civil servants and business – are working from home. Cybercriminals have seized on this to penetrate home computers and steal secrets and access bank accounts. Business and governments need chief information security empowered with budgets and the authority to be logging what’s happening on their network while identifying suspicious activity so they can report it and shut it down.
Third, we need to take what the US National Security Agency calls “defense in-depth”, a layered approach to security that begins with fixing the bugs in the code for the programs operating our basic infrastructure. Today, Perlroth points out, the average high-end car contains more than 100 million lines of code—more than a Boeing 787, F-35 fighter jet, and space shuttle.
Our current system penalizes products with the most secure, fully vetted software. It means a mindset change. The tech sector needs to replace Mark Zuckerberg’s “move fast and break things” mantra with “Move slowly and fix your stuff.” Security engineers need to be brought in from the start to conduct sanitary checks, to vet original code and any code borrowed from third parties. Microsoft and Facebook sponsor an internet-wide bug bounty program to pay hackers cash for bugs they turn over in widely used technology. The European Union sponsors open-source code audits and offers a bug bounty.
Fourth, elections cannot be conducted online. There is not a single online voting platform that security experts have not hacked. Getting ourselves to the polling station and marking our ballot is fundamental to democracy. So is scrutinizing the vote count – machine counts should always be verified with counting by hand.
Fifth, governments at all levels need to use regulatory powers to ensure cybersecurity certification and then enforce those regulations. This means mandates that critical infrastructure operators refrain from using old, unsupported software; that they conduct regular penetration tests; that they don’t reuse manufacturers’ passwords; that they turn on multifactor authentication; and that they airgap the most critical systems.
Regulation is not going to solve the problem but by mandating basic cybersecurity requirements, we can make our critical infrastructure more resilient to a cyberattack. This should include vetting the developers and making compulsory training and certification exams in secure programming. It also means redesigning computer chips from the inside out, adding contamination chambers that would keep untrusted or malicious code out. Why not, writes Perlroth, deploy our best hackers to find and patch vulnerabilities in the nation’s most critical code for one year and then devote a second year to working with IT administrators to secure their systems.
Sixth, it starts with personal responsibility. The vast majority of cyberattacks—98 percent—start with phishing attacks. At the most basic level, says Perlroth, the easiest way to protect ourselves is to use different passwords across different sites and turn on multifactor authentication whenever possible.
In Canada, the annual reports of the National Security and Intelligence Committee of Parliamentarians, drawing on sources including CSIS, CSE, and the Canadian Centre for Cyber Security, have consistently observed that China and Russia are conducting “significant and sustained” foreign interference activities in Canada. Their most recent report (June 2022) bluntly concluded that “cyber threats are a significant and pervasive riskto Canada’s national security…affecting Canadians at numerous levels, threatening government systems and services, critical infrastructure providers, financial and health systems, research and academic networks, and sensitive personal information.”
There are no cyber silver bullets. Dealing with our cyber-vulnerabilities will involve compromises to our national security, to our economy, to the daily conveniences we now take for granted. But we need to act because the annual cost from cyber losses now eclipses those from terrorism.
Democracies need to work together on this. Digitally speaking, says Perlroth, the safest countries in the world, those with the lowest number of successful cyberattacks per machine, are actually the most digitized. The best prepared are the Nordic nations – Norway, Denmark, Finland, Sweden – and the Baltics – Latvia, Estonia and Lithuania – as well as Taiwan. Their governments and commercial sectors have made cybersecurity core to their training and corporate culture.
Civic education is also important. Perlroth cites Harvard’s Joe Nye, who remarked after the investigation into the 2016 US election revealed Russian interference: “The defense of democracy in an age of cyber information warfare cannot rely on technology alone.”
Need more convincing about the dangers of our lack of cyber-preparedness? Look at the Centre for Strategic International Studies log of significant cyber-attacks. It’s a depressing reminder of our cyber-vulnerabilities. We need to read Perlroth’s reporting and heed her advice. Otherwise, Cybermageddon really may be how our world ends.